For years, security was treated as something to fix after products shipped or incidents occurred. That approach worked—until connected systems became mission-critical. High-profile failures like Stuxnet and the Colonial Pipeline attack revealed how insecure design decisions could halt operations, erode trust, and create massive business fallout.
In response, leading organizations changed course. By embracing “Secure by Design”, companies such as Siemens, Azure Sphere, and Medtronic embedded resilience from the start—enabling faster market entry, lower remediation costs, stronger customer trust, and a lasting competitive advantage.
In this environment, security is no longer an optional afterthought or a patch applied at the end of development. It must be a core design principle. “Secure‑by‑Design” embeds protection into the DNA of a product from the outset — enabling smoother market acceptance, stronger customer trust, and long‑term competitiveness in a world where resilience is the new baseline expectation.
What “Secure by Design” Really Means
- Security is considered a design constraint on par with functionality, performance, and usability.
- It must be planned for and upheld at every stage of the product lifecycle: architecture, hardware, firmware, software, communications, and maintenance.
- For industrial products — where hardware, embedded firmware, and connected systems interact in complex ecosystems — “Secure‑by‑Design” ensures risk identification, threat modelling, and protective measures are ingrained into engineering.
Lessons in Critical Infrastructure Security: Colonial Pipeline Ransomware
In May 2021, the Colonial Pipeline, supplying nearly half of the U.S. East Coast’s fuel, was hit by ransomware. Attackers exploited a compromised VPN account without multi‑factor authentication, forcing a shutdown for several days.
Impact:
- Widespread fuel shortages and price spikes
- Economic disruption across multiple states
- Heightened regulatory scrutiny and new U.S. cybersecurity directives
Lesson: Weak security practices in critical infrastructure can trigger national‑level crises, underscoring the need for “Secure‑by‑Design”.
Source : Wikipedia
Why “Secure by Design” Matters for Market Access and Trust
- Europe: The Cyber Resilience Act (CRA) requires products with digital elements to demonstrate strong cybersecurity throughout their lifecycle — from design to end‑of‑life support. Evidence such as risk analyses, technical documentation, product identification, and vulnerability disclosures is mandatory.
- United States: The NIST Cybersecurity Framework and FDA guidance for medical devices emphasize early integration of security and ongoing vulnerability management.
- Global Standards: ISO/IEC 62443 for industrial automation and ENISA guidelines reinforce Secure‑by‑Design as a global expectation.
Secure‑by‑Design makes compliance easier: when risks are identified early and controls baked into architecture, producing evidence, passing audits, and managing lifecycle risks become streamlined. This proactive approach isn’t just about avoiding penalties — it ensures smooth market entry, stronger customer trust, and sustainable competitiveness.
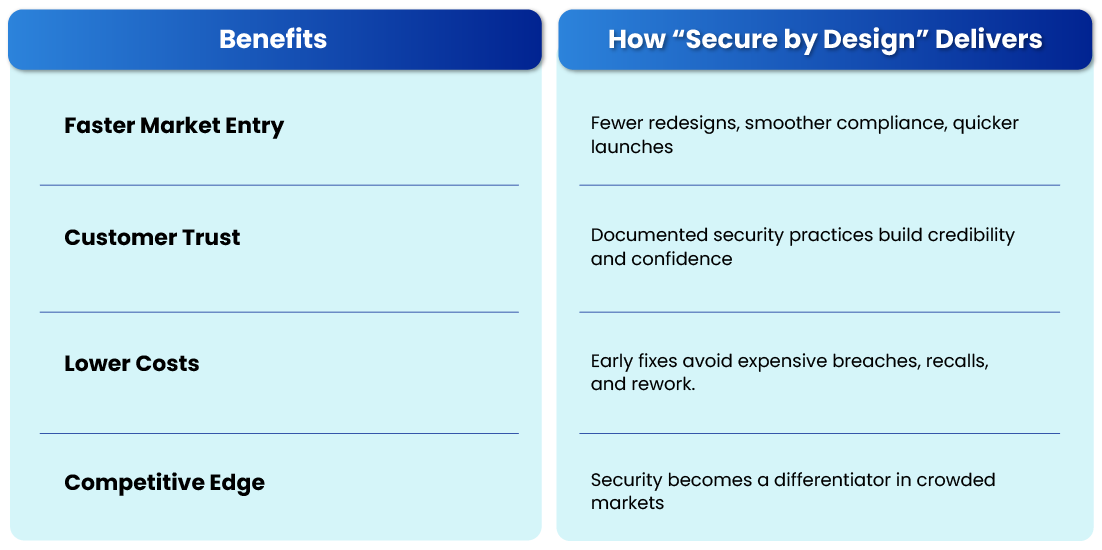
Business Benefits Beyond Compliance
Practical Steps to Embrace “Secure by Design”
1. Assess current product security maturity
2. Integrate security early in development
3. Document and demonstrate compliance
4. Plan for lifecycle support
Two Industrial Leaders Embedding Secure by Design
ABB embeds cybersecurity requirements into the development of its robotics and distributed control systems, aligning products with IEC 62443 standards. By integrating secure firmware, authenticated communications, and vulnerability management processes, ABB supports compliance readiness while maintaining reliability in industrial operations.
Bosch Rexroth – Industrial IoT Platforms
Bosch Rexroth integrates security into the architecture of its industrial IoT and automation solutions, aligning with IEC 62443 and product security lifecycle practices. This enables customers to deploy connected machinery with confidence, meeting regulatory requirements while accelerating digital transformation initiatives.
Why Engineering Partners Matter in Achieving Secure by Design
From a technical standpoint, industrial and connected product ecosystems involve hardware, embedded firmware, and cloud integrations. Partners who understand these layers help identify vulnerabilities that may otherwise remain hidden.
Beyond technology alone, mapping technical controls to regulatory security isn’t just about implementation — it’s about proving compliance. Skilled partners translate technical requirements into regulatory expectations, ensuring documentation, risk registers, and SBOMs align with frameworks like the EU Cyber Resilience Act or ISO/IEC 62443.
Equally important is execution, as operationalizing secure practices by embedding security into daily workflows is often the hardest step. Partners provide playbooks, training, and tools that make secure coding, threat modelling, and vulnerability management part of routine development rather than one-off exercises.
As a result, instead of adding overhead, the right support integrates seamlessly with engineering processes. This empowers product teams to innovate confidently, knowing that resilience and compliance are built in from the start.
Ultimately, many organizations find that partnering with specialists helps them move faster, avoid costly missteps, and build trust with regulators and customers alike.
How Utthunga Helps in this Acceleration
- Security-First Engineering: Deep product engineering and digital engineering expertise ensures security is built into architecture, design, and development—not added later.
- End-to-End Industrial Solutions: From product engineering to IIoT, automation, and digital platforms, Utthunga delivers integrated solutions with security embedded across the lifecycle.
- Secure IT-OT Integration: Proven capabilities in industrial automation and IIoT ensure secure, reliable connectivity between operational and enterprise systems.
- Compliance-Ready & Market-Focused: Strong alignment with industry standards and certifications helps products meet regulatory requirements and enter markets with confidence.
- Proven Industrial Trust: A strong track record with global industrial customers reinforces reliability, resilience, and long-term trust.
Contact us now to know more about our services.