Virtual Commissioning and the Engineering Advantage in Greenfield Facilities
Key Points at a Glance
Greenfield projects leave little room for late discovery. Virtual commissioning shifts automation validation into the engineering phase, where fixes are faster, cheaper, and far less disruptive. This blog explains how virtual commissioning reduces startup risk by testing control logic, sequences, interlocks, and alarm behavior before physical equipment is live. It shows why most early commissioning delays originate in automation, not hardware, and how early simulation prevents those issues from surfacing on site.
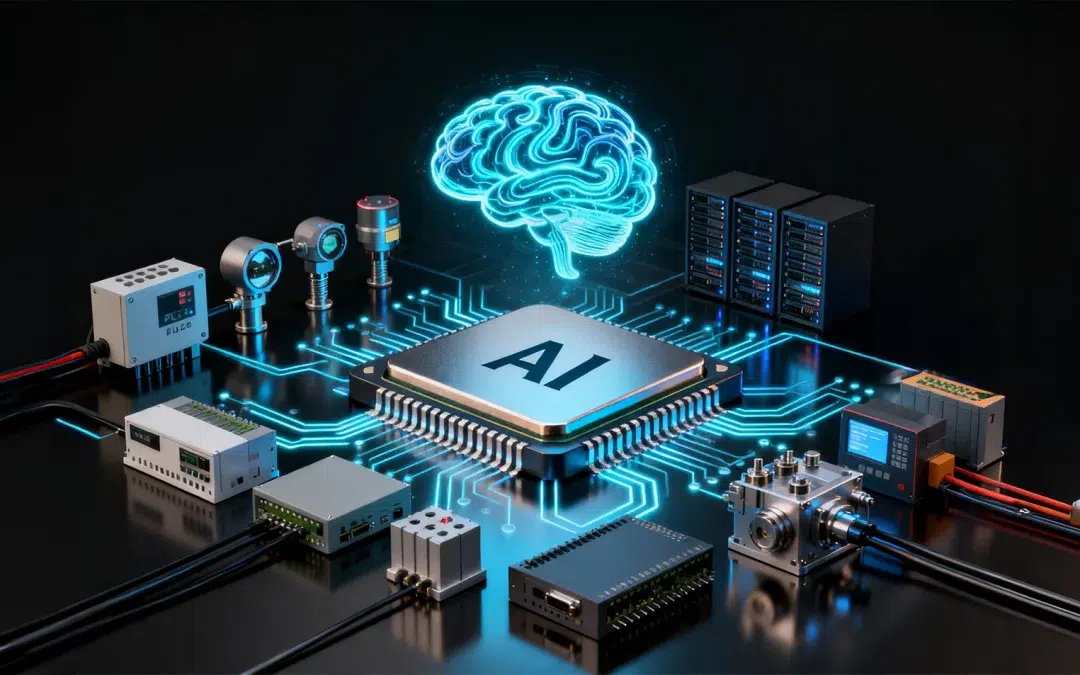
Why Virtual Commissioning Matters for Greenfield Projects
What this really means is that every core automation assumption is examined early. Process intent, mechanical capability, and instrumentation feedback converge in a single model, giving engineers a deeper understanding of how the system will behave under real load conditions.
For greenfield work, this is powerful. It places engineering accuracy on the front seat instead of leaving it for late stage troubleshooting.
Shifting Risk to the One Phase Where Fixes Are Easy
Engineers can run stress tests, step responses, trip scenarios, and interlock verification repeatedly until the behaviour matches the design basis. The result is a logic package that enters site commissioning with significantly fewer unknowns. The impact is measurable: less field troubleshooting, fewer hot work interventions, reduced re-design cycles, and smoother handoff between engineering and operations. As a result, the commissioning phase becomes a confirmation exercise instead of a firefighting exercise.
Reducing Start Up Time Through Early Validation
Virtual commissioning catches these issues at a point when they do not interfere with construction or installation work. Start up sequences, trip responses, load transitions, and alarm priorities are exercised in detail. By the time live commissioning begins, teams focus on verifying physical behaviour rather than unraveling logic inconsistencies. Plants achieve stable operating conditions faster because the automation layer has already gone through extensive stress testing.
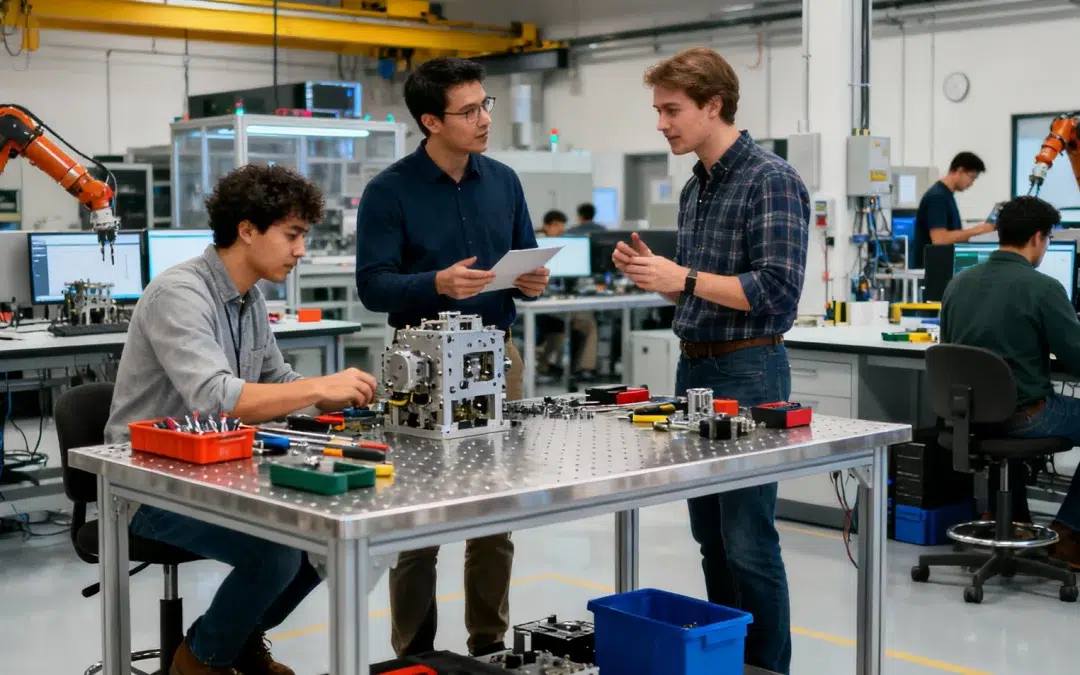
Improving Collaboration Across Engineering Disciplines
If a tank alarm triggers too late, everyone sees it.
If a pump fails to start because of a missing permissive, it becomes obvious.
If two systems accidentally demand power at the same instant, the simulated load profile reveals it.
This reduces the classic handover friction that often slows down large plants.
Building Operator Confidence Before the First Day of Production
It is one of the simplest ways to strengthen human readiness without waiting for physical equipment.
Supporting a Cleaner Transition from FEED Into Detailed Engineering
The benefit compounds. Fewer RFIs, fewer late revisions, and fewer field adjustments create a more controlled construction and commissioning cycle.
The Bottom Line
Utthunga has been bringing this discipline into automation and engineering programs across oil and gas, chemicals, discrete manufacturing, utilities, and infrastructure. Our work in plant engineering, industrial automation services, and systems engineering gives project teams the kind of simulation and integration support that exposes issues long before commissioning day. The goal is simple. A cleaner start up and a plant that performs the way it was meant to from the first hour of operation.
If you want to explore how virtual commissioning can strengthen your next project, reach out to us.